-
Notifications
You must be signed in to change notification settings - Fork 4.9k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Kicbase: update cri-o packaging sources #19504
base: master
Are you sure you want to change the base?
Conversation
 JanGutter
commented
JanGutter
commented
Aug 25, 2024
- cri-o packages have moved to pkgs.k8s.io: https://kubernetes.io/blog/2023/10/10/cri-o-community-package-infrastructure/
- The new packaging format depends on some k8s distro packages. This makes the assumption that the most recent stable k8s is expected to work with the most recent stable cri-o.
- Since cri-o is also installed in the Kicbase/ISO via a different method, further work might still be needed for that case: Add matching Kubernetes Version for crictl to the preload #18359
* cri-o packages have moved to pkgs.k8s.io: https://kubernetes.io/blog/2023/10/10/cri-o-community-package-infrastructure/ * The new packaging format depends on some k8s distro packages. This makes the assumption that the most recent stable k8s is expected to work with the most recent stable cri-o. * Since cri-o is also installed in the Kicbase/ISO via a different method, further work might still be needed for that case: kubernetes#18359
|
[APPROVALNOTIFIER] This PR is NOT APPROVED This pull-request has been approved by: JanGutter The full list of commands accepted by this bot can be found here.
Needs approval from an approver in each of these files:
Approvers can indicate their approval by writing |
|
Welcome @JanGutter! |
|
Hi @JanGutter. Thanks for your PR. I'm waiting for a kubernetes member to verify that this patch is reasonable to test. If it is, they should reply with Once the patch is verified, the new status will be reflected by the I understand the commands that are listed here. Instructions for interacting with me using PR comments are available here. If you have questions or suggestions related to my behavior, please file an issue against the kubernetes-sigs/prow repository. |
|
Can one of the admins verify this patch? |
|
I'd be happy to chat on slack, or open an issue, if needed. |
|
Note that the new packages are only available for "new" versions of Kubernetes. https://kubernetes.io/blog/2023/10/10/cri-o-community-package-infrastructure/ So versions 1.24-1.27 still use the old repo, versions 1.28-1.31 use the new repo(s). New packages contain the same binaries as the github releases / GCS Replacing the other packages such as podman will take more effort, and to fix the bugs...
It would also be good if podman could be updated from 3.4.x to 4.9.x, even it not required. |
Podman needs a way out of "experimental" in the roadmap. This sort-of involves also the CRI-O container runtime, at least as long as they share image storage So that is something for https://minikube.sigs.k8s.io/community/ There is also some discussion in the upstream Kubernetes project SIGs, if it is "included" in the k8s release. |
| @@ -101,6 +101,11 @@ var ( | |||
| `kubernetesVersion:.*`: `kubernetesVersion: {{.LatestVersionP0}}`, | |||
| }, | |||
| }, | |||
| "deploy/kicbase/Dockerfile": { | |||
| Replace: map[string]string{ | |||
| `ARG KUBERNETES_VERSION=.*`: `ARG KUBERNETES_VERSION="{{.StableVersion}}"`, | |||
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
The kicbase cannot have a single kubernetes version, if it is going to be reused for multiple versions.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Would it work for more cases if this kubernetes sources.list is then replaced by later tooling, when the specific version of k8s is installed?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
The easiest would probably be to install the CRI adapter with the Kubernetes components (like cri-tools/cni-plugins/kubeadm/kubelet/kubectl) - possibly split it out into per container runtime, like the "preload" is now?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
It seems like CRI-O now uses an internal bundling of crun and conmon, so it doesn't use the system installation of those anymore,,, Otherwise such shared things could go with the OS installation still, if not k8s-version specific.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Heh, the yak shaving continues (the path that led me here is quite convoluted already!), I'll check out the preload alternative.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Added CRI-O to the discuss items for today's meeting, since there was already some WIP PR for it
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Experimented with building static podman with Nix, similar to the cri-o packaging... (discussion)
That sounds like a bug, the cri-o package should not have any hard dependencies towards kubernetes packages.
That is not currently the case, the stable k8s was tested with a prerelease of cri-o. Users are supposed to use stable. |
Yeah, that's probably due to my misinterpretation of the instructions at https:/cri-o/packaging
My assumption stemmed from the same source: it looks like they list the latest stable series of k8s (1.31) plus the latest stable series of cri-o (1.30) in the example, leading to my assumption that this is expected to work. |
The old repos went through a bit of instability a month or so ago - incidentally, this was one of the reasons I started going down this rabbit hole. |
There has been a lot of stability issues with OBS packages over the years. I think that the new kicbase packaging is unlikely to use the pkgs.k8s.io. Probably go for something similar to dl.k8s.io instead, also for cri-o artifacts.
See https:/cri-o/cri-o/releases for the available versions in GCS. |
|
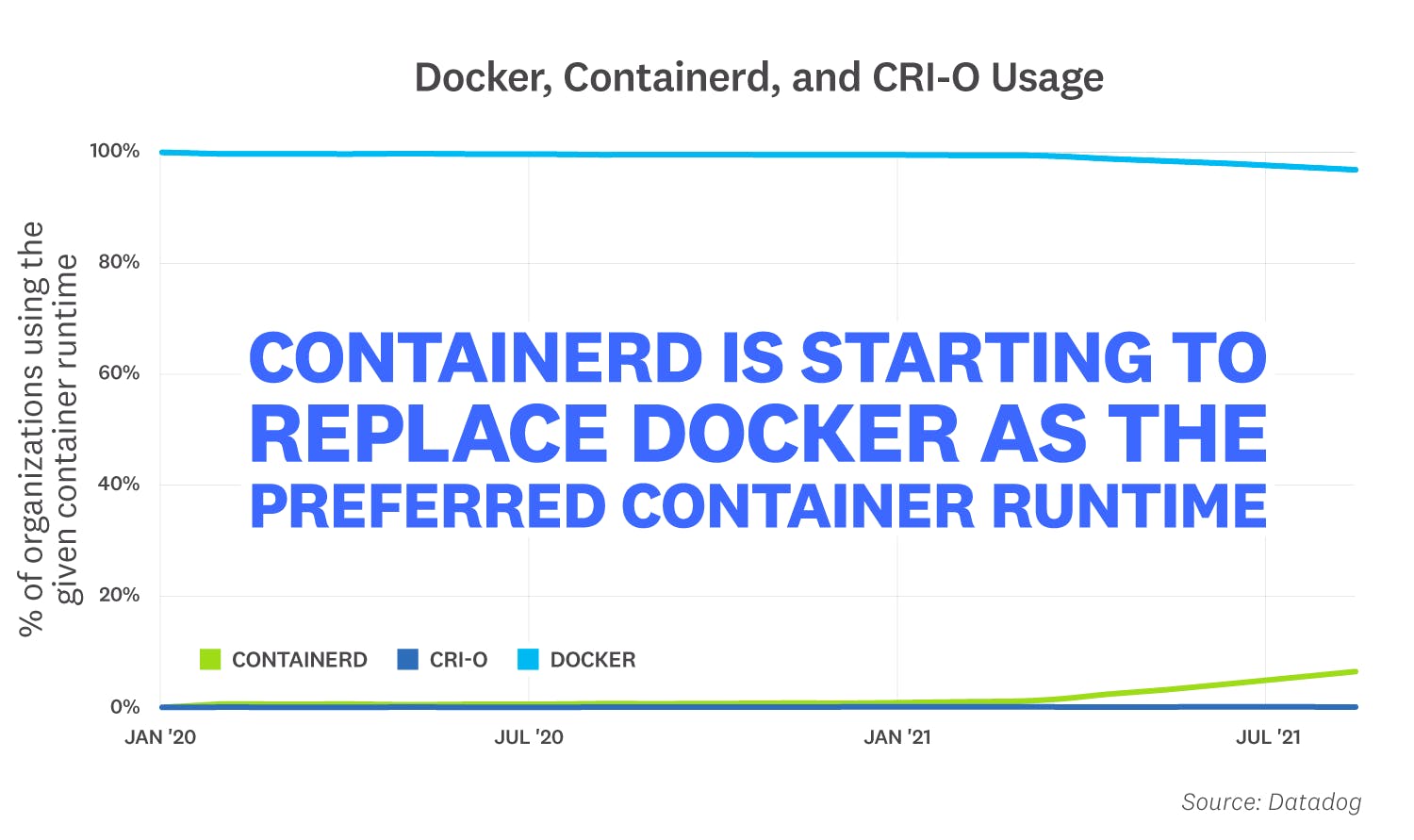
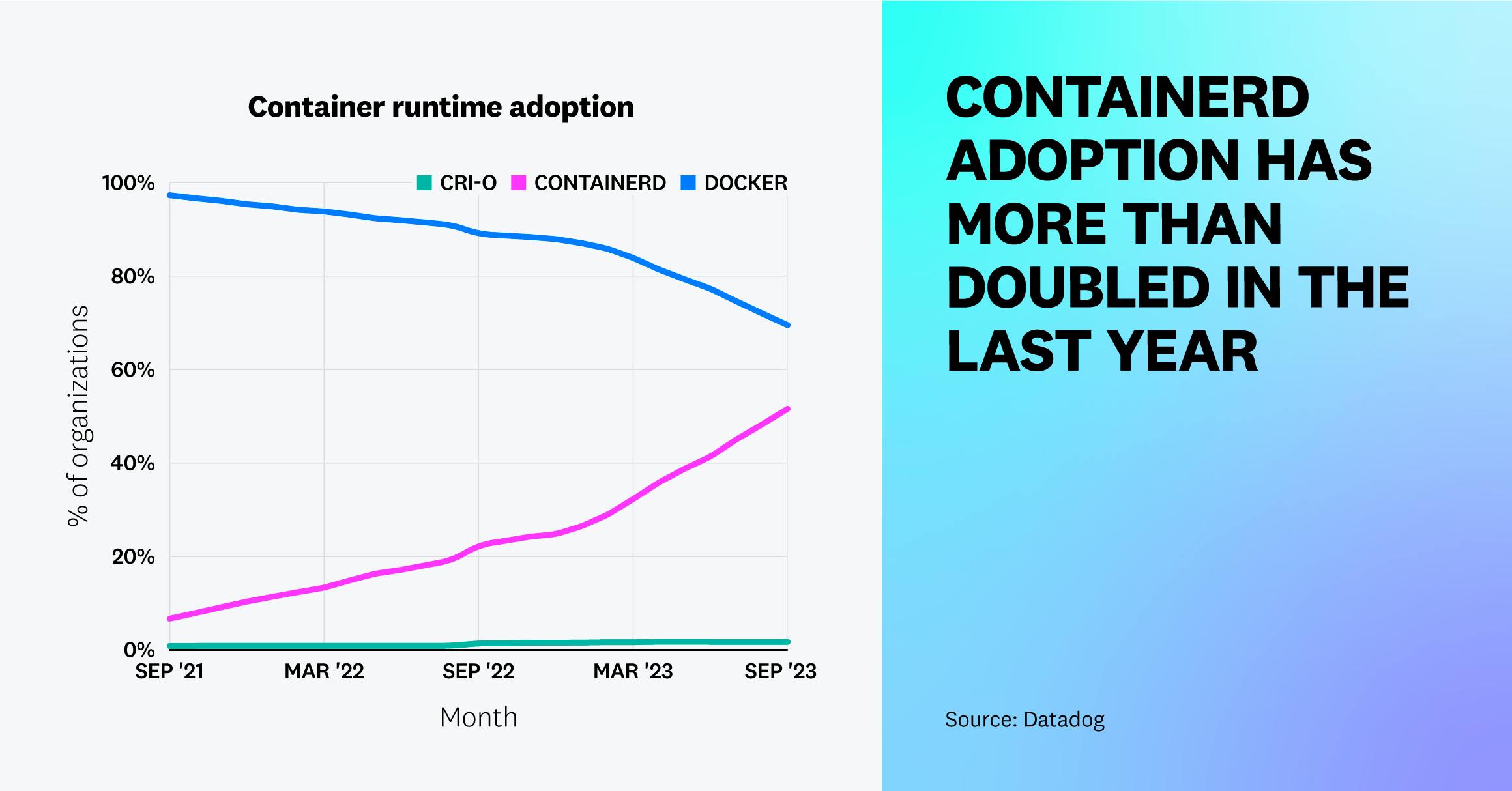
Added this PR for discussion in the community meeting and the office hours, if cri-o should be prioritized... Last time, we added improved support for Podman to the minikube roadmap - maybe also add CRI-O too ? 2021 datadog: https://www.datadoghq.com/container-report-2021/ 2023 datadog: https://www.datadoghq.com/container-report/ You can clearly see cri-o being utilized more, right ? Like the Linux desktop... https://linux.slashdot.org/story/24/08/01/2029219/linux-hits-another-desktop-market-share-record |
|
Oh man, slashdot is still going! This whole rabbithole started when I tried to get a minimal cluster running with centos 9, podman and an ingress. The nice feature of cri-o was that I could configure registry mirrors to rewrite both docker.io and quay.io fqdn paths, so with a CI job and no manifest rewrites, I could do a test of a kubernetes operator and a number of containers. |
|
(This open issue put me on the path to podman moby/moby#18818 ), I'll have to check if containerd's rewrite options are similar. Honestly, if containerd for rootful and rootless podman works better, I'm much less interested in getting cri-o to work. |
| # cri-o depends on some kubernetes packages, the latest stable series | ||
| # is a reasonable choice. | ||
| ARG KUBERNETES_VERSION="v1.31.0" | ||
| ARG CRIO_VERSION="v1.30" |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I dont think we are ready to bump to the latest crio version yet (till we make a preload tarbal to include the critctl and other binaries)
|
PR needs rebase. Instructions for interacting with me using PR comments are available here. If you have questions or suggestions related to my behavior, please file an issue against the kubernetes-sigs/prow repository. |